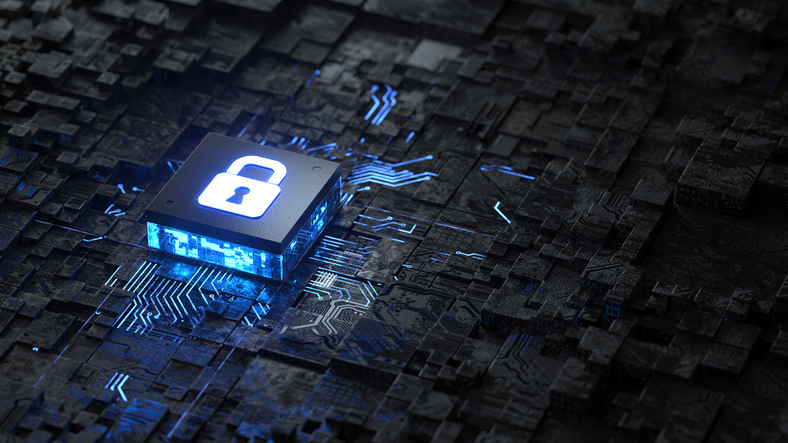
Small business owners have been warned to step up their computer security processes as ‘ransomware’ attacks become more prevalent and sophisticated.
Cyber security experts have dubbed 2016 the Year of Ransomware with attacks that lock computer databases increasingly targeted at Australian businesses.
Small to medium businesses could be more vulnerable to attack, a Perth academic warned if multiple users had administrator access and cyber-security was not a priority. “We see a news item almost every day of the week (on ransomware),” said Dr Zubair Baig, senior lecturer in cyber security at Edith Cowan University’s School of Computer and Security Science. “It’s a major issue these days. I see this as a serious threat to enterprises. Frequently it’s naïve users – people who don’t know how to secure a machine or a bunch of machines in a small or medium enterprise – that are the first victims,” Dr Baig tells us.
“Essentially anybody who would be willing to open an email attachment would be vulnerable.” Ransomware, he explained, did not involve stealing data. But rather, was a virus that encrypted files (including client databases) on host computers. This effectively locked the information until a ‘ransom’ was paid in return for a decryption key. The virus was commonly delivered via scam email attachments and could be crippling to businesses.
In March 2015 the Australian Federal Police issued a warning after a ransomware email purporting to be an AFP subpoena was delivered to thousands of Australians.
Cybercriminals usually demanded the equivalent of $400-500 in untraceable cryptocurrencies, such as BitCoin. “$500 per victim and multiply that by 10 victims a day – that’s $5,000,” Dr Baig said. It was affordable for victims but generated significant income for scammers. “The business model works out perfectly, and the trails are concealed so we can’t actually find out who carried out the attack.”
A report released last year ranked Australia second only to the US in the number of ransomware attacks, with the numbers of attacks on businesses rather than individuals jumping from 16 per cent in 2014 to 28 per cent in 2015. The Tasmanian Chamber of Commerce and Industry has revealed it was hit by an attack and paid a ransom of AU$460 in 2015.
Many businesses reason that paying the ransom is cheaper and faster than paying IT experts to ‘crack’ complex encryption codes. The Australian Competition and Consumer Commission received more than 2,500 complaints about ransomware last year, with an estimated $400,000 paid to attackers. However, a spokeswoman told ABC News this was the tip of the iceberg, as many attacks went unreported.5 Experts warn ransomware attacks are becoming more sophisticated, skimming social media accounts to deliver personalised mail attacks. In March, security firm MailGuard reported an email that appeared to be parcel delivery notifications from Australia Post.
Those who opened “tracking details” found their computers locked and a ransom demanded. The sudden explosion in ransomware was due to a confluence of technological advances, Dr Baig said.
The advent of cryptocurrencies, such as BitCoin, provided untraceable payment methods, while greater connectivity increased the vulnerability of computer systems. The ‘Tor’ network or ‘dark web’ also allowed cybercriminals to hide the source of emails, minimising the risk of being caught. Dr Baig and his colleague Nikolai Hampton found more than 80 per cent of recent ransomware strains were using advanced security features, which made them difficult to detect, and advanced encryption, which rendered them practically impossible to ‘crack’.
But despite the increasing sophistication of ransomware, Dr Baig said attacks were not difficult to prevent or mitigate if SMEs followed some simple steps to stay on top of online security. The Federal Government intends to offer grants of up to $2,100 for small businesses to have their cyber security professionally vetted (applications open in the 2017/2018 financial year).
To protect against ransomware attacks (Courtesy Z Baig and N Hampton, Edith Cowan University)
- Don’t fall prey to social engineering or phishing, which is where an attacker attempts to have you reveal sensitive information to them. If you receive a suspicious email from your grandma or work colleagues, ask yourself whether it’s unusual before you click. If you’re not sure, contact the sender via a different medium, such as giving them a phone call, to crosscheck.
- Don’t install any software, plugins or extensions unless you know they’re from a reputable source. If in doubt, ask and only rely on trusted download sources. And certainly, don’t be tempted to pick up USB sticks found on your pathway.
- Update your software (comprising your operating system, web browser and other installed software) regularly to ensure you are always running the latest versions.
- Backup! Important documents need to be treated like valued possessions. Grab a handful of USB keys and rotate your backups daily or weekly, and don’t leave USB keys plugged in (current malware strains can scan removable USB disks). Having multiple copies means the adversarial effort of holding you for ransom is pretty much worthless.
- Use reputable network defence mechanisms. A software firewall and anti-malware are advisable to regularly scan your machines looking for vulnerabilities and plugging holes at the right time.