Check out the below article, it’s an example from our SMART Business Newsletter, Insights.
Want to know more about how you could have your own customer newsletter for business and residential customers? Check out what SMART can offer you.
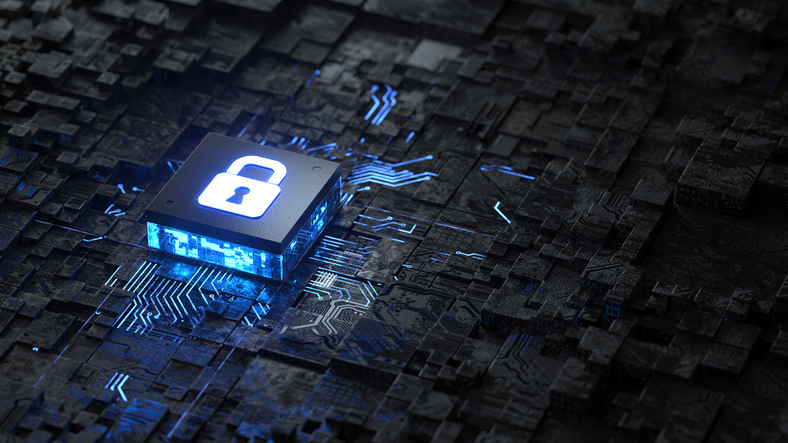
Systems under strain
Help prevent ransomware attacks at the source by knowing what weaknesses common malware exploits to gain entry.
The key to commercial success is scalability. Unfortunately for law-abiding businesses, cybercriminals have clued on to this, with Malware as a Service (MaaS) and Ransomware as a Service (RaaS) sending computer hacking through the roof.
Once upon a time, only the most skilled and well-funded hackers could launch attacks on businesses. But recently, malware developers began offering subscription-style services that provide access to hacking software, tools, technical support and even product updates that allow low-skilled criminal enterprises to launch their own lucrative attacks.
Since 2020, it’s taken cybercrime from fine dining to fast food in terms of accessibility and prevalence, according to one commentator. And it means legitimate software developers are racing to keep pace with malware adversaries looking for vulnerabilities in their systems. The Australian Cyber Security Centre (ACSC) and the US’s Cybersecurity and Infrastructure Security Agency (CISA) recently published a joint security advisory detailing the top malware strains plaguing Australian computers.
Ransomware vs Malware
First, what is the difference between ransomware and malware? Malware – a portmanteau of malicious software – is the initial program used to gain access to a device or network. Once the malware is installed, it can be used to covertly steal data or deliver ransomware, which encrypts or locks access to vital data until a ransom is paid. Because malware is the first step in a more devastating attack, it’s important businesses understand the key threats.
The most common types of malware in Australia are Trojans and Remote Access Trojans (RATS). As the name implies, Trojan malware is disguised as a legitimate download, such as a game launcher or installer, which is why advice stresses only trusting downloads from official sources.
The most common malware, according to ACSC and CISA are:
Agent Tesla
- Type: RAT.
- Details: Capable of stealing data from mail clients, web browsers and FTP servers. Personal information and logins are often sold on the dark web.
- Delivery method: An attachment in phishing emails.
AZORult
- Type: Trojan.
- Details: Used to steal browser data, user logins and cryptocurrency information.
- Delivery method: Phishing attachments or downloads on compromised websites.
FormBook
- Type: Trojan.
- Details: Capable of key logging to capture passwords.
- Delivery method: Attachment in phishing emails.
Ursnif
- Type: Trojan.
- Details: Also known as Gozi, Ursnif is a banking Trojan that captures financial information. It uses key extraction tools to access encrypted files.
- Delivery method: Attachment in phishing emails.
LokiBot
- Type: Trojan.
- Details: It focuses on stealing user credentials, cryptocurrency wallets and other passwords and logins.
- Delivery method: Usually an email attachment, but a variant has been disguised as a Fortnite multiplayer launcher.
MOUSEISLAND
- Type: Macro downloader.
- Details: This malware is usually found in the embedded macros of a Microsoft Word document. An old trick that has new legs as a ransomware vehicle, malware such as MOUSEISLAND is why experts recommend disabling macros in Word.
NanoCore
- Type: RAT.
- Details: This is used to steal passwords and infiltrate emails. It can also be used to activate webcams to spy on victims.
- Delivery method: It has been delivered in an email as an ISO disk image within ZIP files and in malicious PDF documents.
Want to deliver content to engage and help your customers?
AFG’s multi-award-winning SMART platform is designed for brokers who want to see their business soar.
What to do?
As this list demonstrates, malware that can result in data theft or a ransomware attack begins with an employee clicking a compromised link. There are very simple steps every business can take to protect themselves immediately.
- Educate: Ensure all your staff understand social engineering tricks used in phishing emails that may lure them into clicking a malware link. Stay alert for symptoms of a malware intrusion.
- Update software: Businesses must prioritise patching. The ACSC has advice on frequency and recommends if resources are constrained, to ensure all internet-facing services are up to date first, followed by important network devices, servers and workstations of high-risk users (senior managers, administrators, and staff members from human resources, sales, finance and legal), then all other devices.
- Backup: Always keep offline data backups regularly updated.
- Disable Microsoft Office macros: Macros are small programs used to automate simple tasks in Microsoft Office documents but can be used maliciously – visit the Microsoft website for information on disabling macros.
- Stay in the loop: Sign up for the ACSC’s Alert Service and partnership program for SMEs.
- Use multi-factor authentication and passphrases: These two simple steps make a business’s systems more secure. Use random, rather than commonly linked words, such as idioms or lyrics.